This article is more than 1 year old
Lenovo shipped lappies with man-in-the-middle ad/mal/bloatware
'Superfish' causes an almighty stink
Lenovo is in hot water after being caught intentionally shipping laptops with software that steals web traffic using man-in-the-middle attacks.
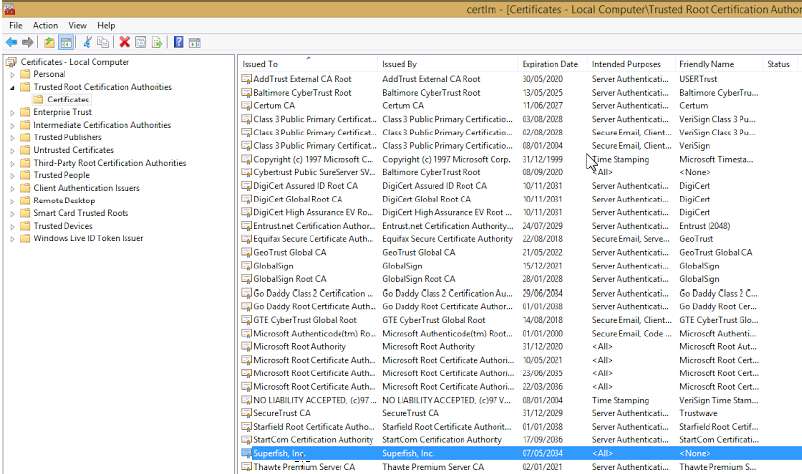
The "Superfish" software was present on laptops sold until late last month and stole all manner of web traffic using fake, self-signed, root certificates to inject advertisements into sessions.
Vulture South has contacted Lenovo and Superfish for comment.
The computer giant removed Superfish software after furious users reported the attacks on its forums.
One screenshot taken by an unhappy user shows a certificate masquerading as being issued by Bank of America.
Another user posted a purported screenshot of the program showing it as a trusted root certificate and claiming a web connection to their bank was intercepted.
"A blatant man-in-the-middle attack malware breaking privacy laws. I have requested return of the laptop and refund as I find it unbelievable that ... Lenovo would facilitate such applications pre bundled with new laptops," the user wrote on the Lenovo forums.
Forum administrator and Lenovo employee Mark Hopkins said following dozens of angry posts that new laptops will no longer be sold with Superfish. The company has also asked the company behind the program to issue an update squashing pop-up ads.
"Due to some issues (browser pop up behavior for example), with the Superfish Visual Discovery browser add-on, we have temporarily removed Superfish from our consumer systems until such time as Superfish is able to provide a software build that addresses these issues," Hopkins said.
"As for units already in market, we have requested that Superfish auto-update a fix that addresses these issues.
"The technology instantly analyses images on the web and presents identical and similar product offers that may have lower prices, helping users search for images without knowing exactly what an item is called or how to describe it in a typical text-based search engine."
Facebook engineering director Mike Shaver raised the alarm about the ad/bloatware on Twitter, and found SuperFish certificates posted by different users had shared the same RSA key.
"Lenovo installs a MITM cert and proxy called SuperFish, on new laptops, so it can inject ads? Someone tell me that's not the world I'm in," Shaver said.
SuperFish was listed by at least 11 antivirus companies as a potentially unwanted program, adware, or a trojan.
More to come. ®